SOA3 Authorization Module
Overview
Authorization is the function of specifying access rights to resources and enforcing the taken decisions. There are diverse Authorization models: SOA3 Authorization Module bases its decisions on stored policies by which it is able to determine if a subject can perform a certain action on a certain resource. Since the subject is defined by a set of attributes referred to the caller, the call and the environment, the adopted model is defined as Attribute Based Access Control (ABAC) [1]. ABAC is a very flexible model, which can be view as a generalization of Role Based Access Control[2], where the only allowed attributes are roles.
In particular the module:
- receives Authorization Requests containing caller and call related attributes from gCube Security Handler
- evaluates if the caller is authorized to perform a certain action basing the decision on received attributes, environment attributes and stored policies
- returns Authorization Responses to gCube Security Handler
GCube Security Handler could contact SOA3 Authorization Module in different ways: in particular a strict integration could be obtained by using Java Library API or it is possible to have looser dependencies by web service interfaces, SOAP and RESTful. In order to obtain a zero-dependencies model the RESTful interface is used sending the following parameters:
- call and caller attributes, at least user role
- requested service's id, representing the resource in authorization terms
- requested operation's label, representing the action
Key features
- Attribute Based Access Control Model
- a very general and extensible model which base the decisions on a set of attributes from the caller, the call and the environment
- Policy based decisions
- the decisions are based on a set of pre-defined policies stored
- Standard based architecture
- the module is based on the standard eXtensible Access Control Markup Language (XACML) [3]
- Graphical policies management interface
- a portlet is available to define and manage policies
- Extensible set of attributes
- Possibility to configure the attributes set to be used for policies evaluation
- High availability
- redundancy and load balancing for improving performance
Design
Philosophy
A canonical XACML based architecture is composed by:
- Policy Administration Point (PAP)
- Policy Decision Point (PDP)
- Policy Enforcement Point (PEP)
- Policy Information Point (PIP)
The architecture of the Authorization Module is fully compliant with such organization. Some of the required functionalities are provided by the open source software Argus Authorization Framework, while the interaction with gCube Security Handler and the management of dynamic attributes requires dedicated facilities.
Architecture
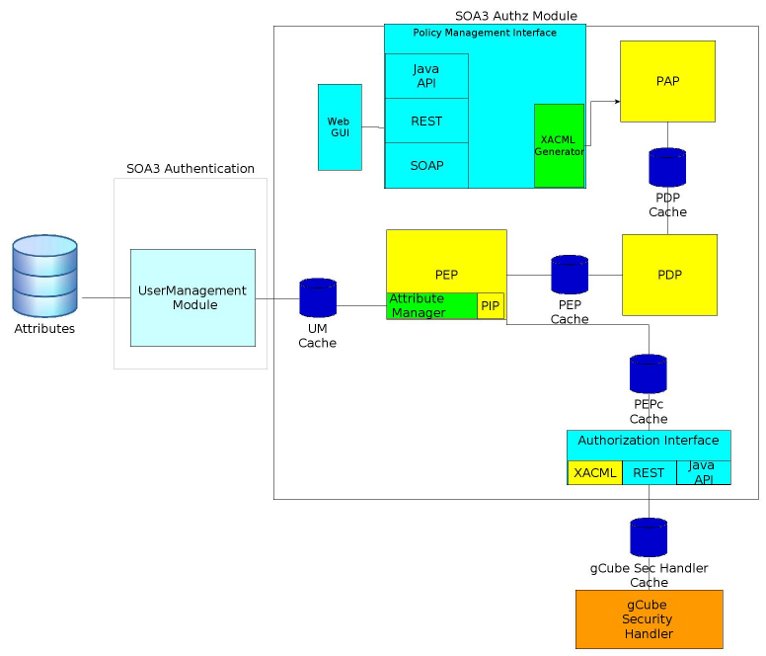
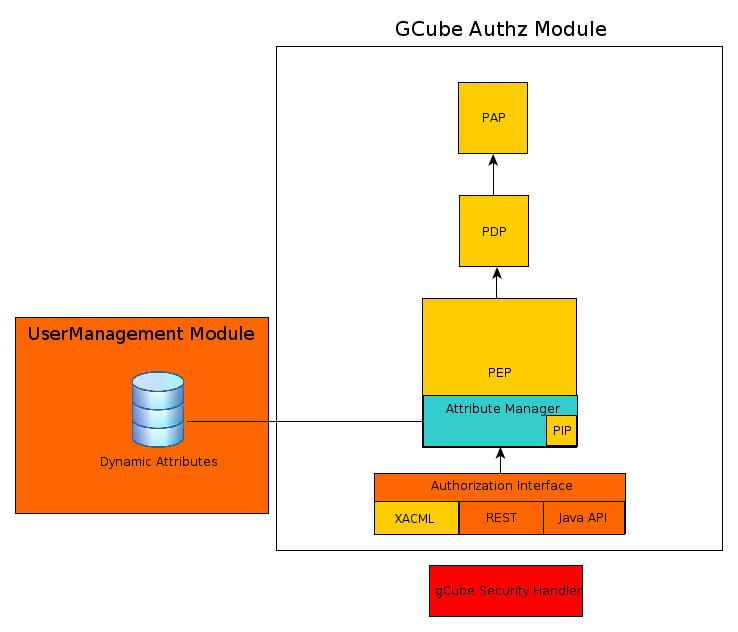
The architecture is depicted in the following figure:
The Authorization Interface element is the contact point between the Authorization Module and the gCube infrastructure. Three kind of interfaces are provided:
- XACML, using the standard protocol request message, in particular SAML2.0 profile of XACML2.0 with SOAP transport
- REST
- Java Api for strict integration of the Authorization module with gCube Security Handler
gCube Security Handler should contact the Authorization System through these interfaces, in particular:
- XACML interface is the same interface exposed by PEP, so it means to contact the PEP directly
- REST interface provides a method which hides all the complexity of the system, allowing only to ask if an user is authorized and receive the response
- Java API means that it is possible to totally integrate the interface in the Request Interceptor as Java Library using some exposed API to contact the PEP
gCube Security Handler flexibility provides the possibility to choice any of these interfaces.
The PEP is a canonical Policy Enforcement Point, which enforces the decision evaluated by the PDP. The element is extended with an internal Attribute Manager which manages two categories of attributes:
- local user attributes
- context attributes
it not only contacts the PEP, but also acts as Dynamic Attribute Manager and Contextual Attribute Manager. The Dynamic Attributes are, for example:
- number of access performed by that user
- last access time
The attributes are accessed through the UserManagement Module by web services in read-only mode. The update operation of dynamic attributes is outside the scope of the authorization system. They should be updated by an external accounting-billing system, since the attributes manager is able only to read these attributes.
The PIP adds contextual attributes, i.e. attributes with no relationship with the user, such as:
- date and time
- virtual organization status
- global infrastructure status
These attributes, called in XACML terminology, environment attributes, are used to take decision based also on external factors. The other components play the same role described above, in particular:
- PDPs elaborate the policy decision
- PAP provides the required policies
Caching and load balancing mechanism are provided to improve the performances and the availability of the system.
- Current status
The current implementation status is the following:
- the PEP is integrated in gCube security Handler by Java API interface, XACML interface is available and REST interface should be completed
- context attribute support will be available during the next steps of the project
- the other functionalities are under test
Deployment
GCube Authorization module should be deployed per Virtual Organization: in particular there should exist a module for each VO and the module should protect all the resources belonging to that VO.
Large deployment
The maximum scalability is obtained using load balancers between PDP and PAP, PEP and PDP and also Authorization interfaces and PEP. The diagram is similar to the architecture diagram above.
Small deployment
A minimal solution is the following:
Use Cases
Since the subsystem is currently under test there are no "success stories" available